Exciting New functionality: FIDO2 for Windows Credential Provider
Exciting New functionality: FIDO2 for Windows Credential Provider
OpenOTP Security Suite is 100% FIDO2 compatible. This means you can log in to your Windows computer with FIDO2 ready USB keys or devices, as you previously did with FIDO U2F Keys.
What is FIDO2?
FIDO2 enables users to easily authenticate to the online services in both mobile and desktop environments.
FIDO2 is the successor to the previous authentication standards, FIDO UAF and FIDO U2F.
Advantages of using FIDO2 for Multi-Factor Authentication
1. Multiple system Authentication with one device
You have the ability to secure web applications as well as desktop log-ins via Multi-Factor Authentication.
2. Higher Security
FIDO2 provides strong user authentication with a keypair (private and public) that can only be unlocked with a finger press. The FIDO standards protect the users against fishing attacks by linking the cryptography to the DNS names.
3. Low Discrepancy
There is a counter stored on both the FIDO key and the relying party (WebADM). It is incremented in the FIDO key each time you get an assertion from it, and that value is sent in the assertion to WebADM which stores it. That new value should always be higher than the one which is already stored in WebADM hence detecting cloned/forged authenticators.
Log in to your Windows computer via the FIDO2 key using 3 scenarios:
- If you are on your Active Directory network, you can log in on your Active Directory with or without enabling Multi-Factor Authentication with your FIDO2 Key.
- If you are outside your network and connected to the internet, you can still authenticated with your FIDO2 key that is verified on the RCDevs OpenOTP Server.
- With no connection at all, the offline mode allows you to use your FIDO2 Key to authenticate on your computer. This mode is, of course, not mandatory and you can set the duration you want to enable it.
How FIDO2 works with the Windows Credential Provider client?
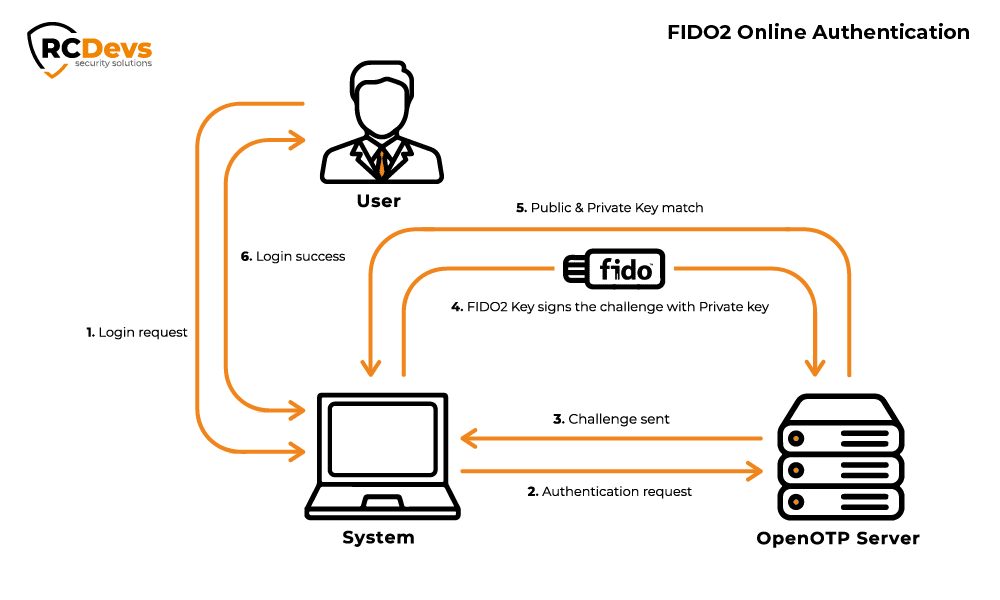
Offline login functions using asymmetric keys, making it impossible to decrypt any information with the public key.
Here WebADM is the relying party. When you login with FIDO2 configured, WebADM sends a challenge to the private key. The user’s private key is stored in FIDO2 authenticator, which is protected by a biometric factor or a pin (user’s presence is mandatory) and is used to sign transactions initiated by the relying party.
It replicates the tree logging scenario you experienced with the RCDevs Mobile Push App onto your Windows login.

