SpanKey SSH Key Server and SSH Key Management
SSH Key Management
SpanKey SSH
Access Server
SpanKey is a core service running within WebADM, RCDevs’ core framework, providing centralized and secure key management
The IT infrastructure for most organizations relies on Linux
and Unix servers.
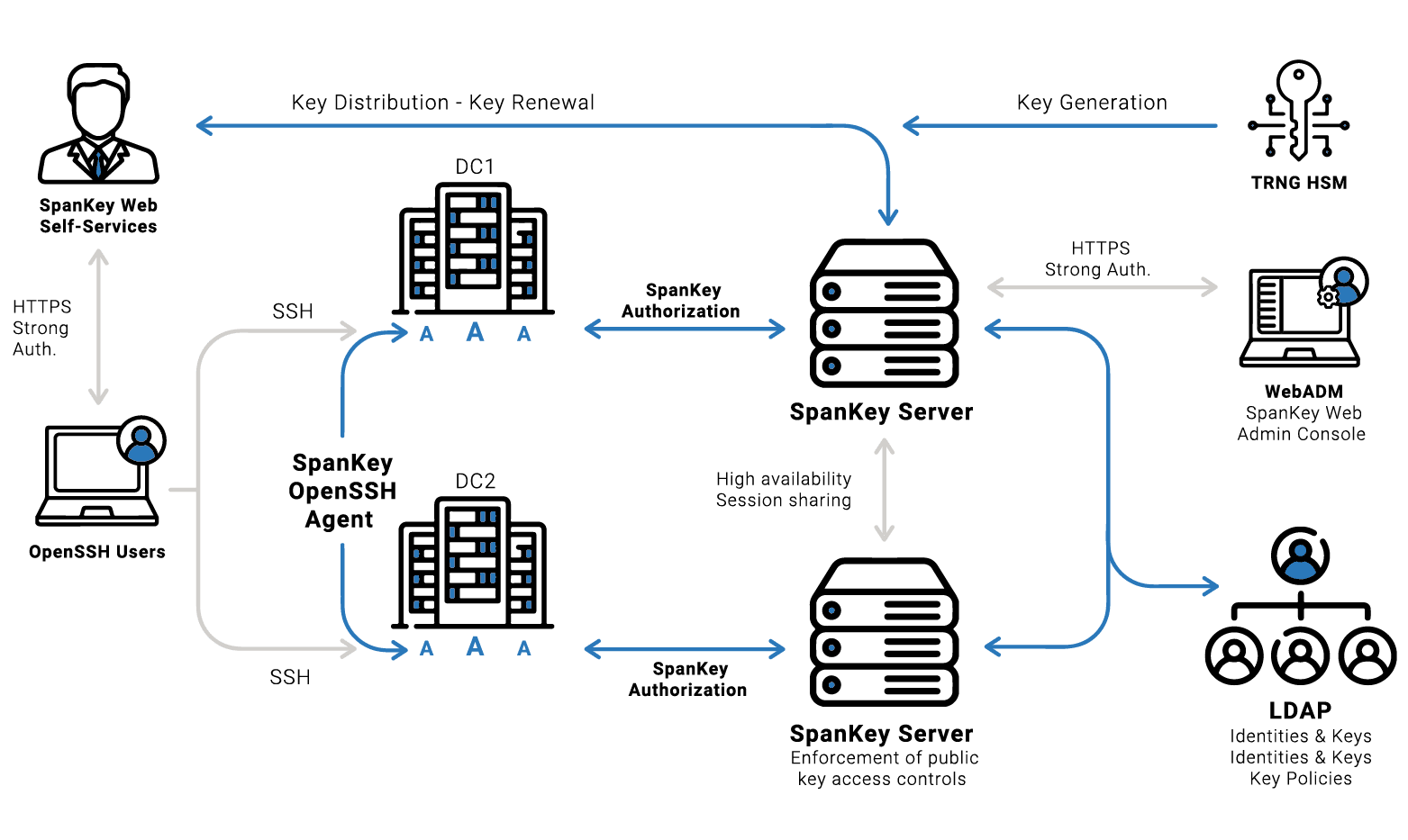
SpanKey Server is part of RCDevs SpanKey solution which provides Linux centralized SSH access management. With SpanKey enabled, you do not need to deploy or maintain SSH keys on Linux servers as the key distribution is controlled by WebADM and the key enrollment is done via the self-services. SpanKey also handles NSS users and groups without the need for LDAP connectivity and provides centralized sudo, session recording, command monitoring and much more.
SpanKey requires the SpanKey agent / client to be installed on the target Linux hosts. SpanKey agent is available as RPM and DEB packages on our online repos.
Linux server access is generally implemented with SSH for both administration and host-to-host scripting. The SSH protocol is secure and extremely convenient for server management.
Adding an extra security layer is recommended for SSH key management with critical/production systems.
RCDevs Security provides these extra layers of security by combining SSH Public Keys and Multi-Factor Authentication (MFA).
Centrally manage SSH Keys
Easy Keys Enrollment with Self-Services
Graphical Session Recording
Automated Public Key Expiration
Conditional Access
Support for Shared Account
Centralized Audit Rules and Logs
Master Keys and Recovery Keys
HSMs & Hardware SSH Devices
SpanKey Server & SpanKey OpenSSH Agent
DEPLOYMENT
Where to use SpanKey
SpanKey runs on your WebADM Cluster and connects to Active Directory (or any LDAP directory).
The Linux agent is available as RPM and DEB packages
Supported platforms
• Debian / Ubuntu
• Suse Linux
• Raspberry Pi/ ARM
Public Key Algorithms
• RSA With 1024, 2048 and 4096 bits
• ECC (Elliptic Curve) With 256, 384 and 521 bits
• DSA With 1024 bits only
SEEING
IS BELIEVING
Whether you are buying a car or a security solution, you always want to test drive it before signing on the dotted line. We know this and you know this.
Contact us for your Free PoC or check it out for yourself.



