
The 2024 Cybersecurity Forecast: AI, IoT Security, and Emerging Challenges
The 2024 Cybersecurity Forecast: AI, IoT Security, and Emerging Challenges
As we’ve entered 2024, the cybersecurity landscape evolved quickly due to technological advancements and emerging threats, emphasizing the importance of understanding upcoming trends for those protecting digital assets. As widely reported, 2023 saw a resurgence in ransomware incidents, with record-breaking monthly occurrences. Additionally, there was an increase in cyber espionage activities. This article aims to provide a comprehensive overview of the cybersecurity trends poised to shape the year 2024, focusing on critical areas such as Artificial Intelligence (AI), Internet of Things (IoT) security, and broader cybersecurity challenges. Our journey through the key cybersecurity trends for 2024 will cover the following:
- The Rise of AI in Cybersecurity
- Advanced Ransomware Techniques and Social Engineering Attacks
- IoT Security Trends
- Cloud Security Developments
- Data Privacy Trends and Regulations
- Passwordless Authentication: Will 2024 Mark the Tipping Point?
- Zero Trust Architecture Implementation
- The Cybersecurity Workforce and Skill Shortage
I. The Rise of AI in Cybersecurity
Artificial Intelligence (AI) in cybersecurity is a rapidly evolving frontier, marked by significant advancements and complex challenges in 2024. As AI becomes increasingly integrated into cybersecurity strategies, it presents a novel landscape where the lines between defense and attack blur, necessitating a nuanced understanding of its capabilities and limitations.
Cyber attackers are increasingly using AI to enhance their tactics, resulting in more sophisticated and hard-to-detect cyber threats. These threats range from using AI for developing malware that can adapt to different environments or employing machine learning to identify vulnerabilities in systems more efficiently, AI-enhanced phishing attacks where AI is used to craft more convincing phishing emails, to AI-powered password attacks that can guess passwords more efficiently. As these AI-powered cyber threats become more prevalent, the cybersecurity community is facing new challenges in detecting and mitigating these advanced attacks.
On the defensive front, the role of AI in cybersecurity is is in its early stages of development. Advanced AI algorithms tend to be employed for a range of purposes, from monitoring network traffic to detecting malware with improved accuracy and speed. These systems are designed to analyze vast amounts of data to identify potential threats, often catching anomalies that human oversight might miss. What’s more, AI-driven automation in incident response hope to revolutionise how organizations respond to cyber threats, promising quicker and more effective mitigation of attacks.
In this context, the proven effectiveness of classical Multi-Factor Authentication (MFA) systems remains a fundamental in the cybersecurity strategy of organizations. These traditional MFA systems, especially when applied to the entire potential attack surface including VPN and Wifi, offer a tried-and-true layer of security that is crucial for protecting digital assets in today’s ever-evolving cyber threat landscape. While AI-driven approaches in cybersecurity are a topic of interest and exploration, they currently supplement rather than replace the foundational security measures provided by robust MFA solutions.
The dual use of AI in both advancing cybersecurity defenses and enhancing cyber attacks highlights the critical need for continuous innovation and vigilance in this field. At RCDevs, we believe that an appropriate reduction of the attack surface through Presence-based Logical Access, coupled with solid cryptographic processes, remains in 2024 the best bulwark against AI-powered cyber threats advances in this field.
II. Advanced Ransomware Techniques and Social Engineering Attacks
Ransomware continues to be a significant threat, with attackers constantly evolving their methods to maximize impact and profit.
The overall trend in ransomware attacks shows a worrying increase. A recent report indicated that ransomware groups launched 514 attacks in just one month, surpassing previous monthly records. This rise in ransomware attacks highlights the increasing complexity and frequency of these dangers. The report also mentioned that ransom payments might exceed $500 million by the end of the year, indicating the financial impact of these cyberattacks.
Social engineering attacks are becoming more refined and convincing, posing a considerable challenge in 2024. Cybercriminals are leveraging psychological manipulation more effectively, often aided by technology, to trick individuals into divulging confidential information or performing actions that compromise security. Organizations must prioritize training and awareness programs to equip employees with the knowledge to identify and resist such deceptive tactics.
We’re seeing a shift towards more sophisticated extortion techniques, far beyond the traditional model of encrypting data for ransom. These advanced tactics include targeting an organization’s clients or partners and using disruptive methods like Distributed Denial of Service (DDoS) attacks alongside traditional ransomware. This evolution necessitates a proactive and comprehensive approach to ransomware defense, going beyond conventional antivirus and backup solutions.
III. IoT Security Trends in 2024
The Internet of Things (IoT) is undergoing an unprecedented expansion, with 2024 set to witness a significant increase in the number and variety of connected devices to reach over 19 billion devices by 2025 according to Statista. This growth, while offering numerous benefits in terms of efficiency and connectivity, also brings with it a host of security challenges that must be addressed.
One of the primary concerns in IoT security is the inherent vulnerability of these devices. Many IoT devices are designed with convenience and functionality in mind, often at the expense of robust security features. This makes them attractive targets for cyber attackers, who can exploit these weaknesses to gain unauthorized access to networks, steal sensitive data, or even use these devices as part of larger botnet attacks.
To combat these risks, a multi-faceted approach to IoT security is essential. First and foremost, there needs to be a shift in the mindset of manufacturers, with an emphasis on integrating security measures right from the development phase of IoT devices. This includes implementing strong encryption, secure authentication protocols, and regular firmware updates to patch vulnerabilities.
Beyond the rapid application of these updates, organizations deploying IoT solutions must take proactive steps to secure their networks. This involves regularly assessing and monitoring the security posture of all connected devices, implementing network segmentation to limit the spread of potential breaches, and employing advanced security solutions like intrusion detection systems that are specifically designed for IoT environments.
Another emerging trend is the use of AI and machine learning in IoT security. This trend, often referred to as the Artificial Intelligence of Things (AIoT), combines AI’s data-driven insights with IoT’s network of connected devices, leading to enhanced security and efficiency.
These technologies can be leveraged to analyze patterns in network traffic, identify anomalies that may indicate a security breach, and automate responses to potential threats.
As we move into 2024, the security of IoT devices and networks will continue to be a critical concern. The combination of technological innovation, strategic security planning, and ongoing vigilance will be key to protecting these ever-expanding digital ecosystems.
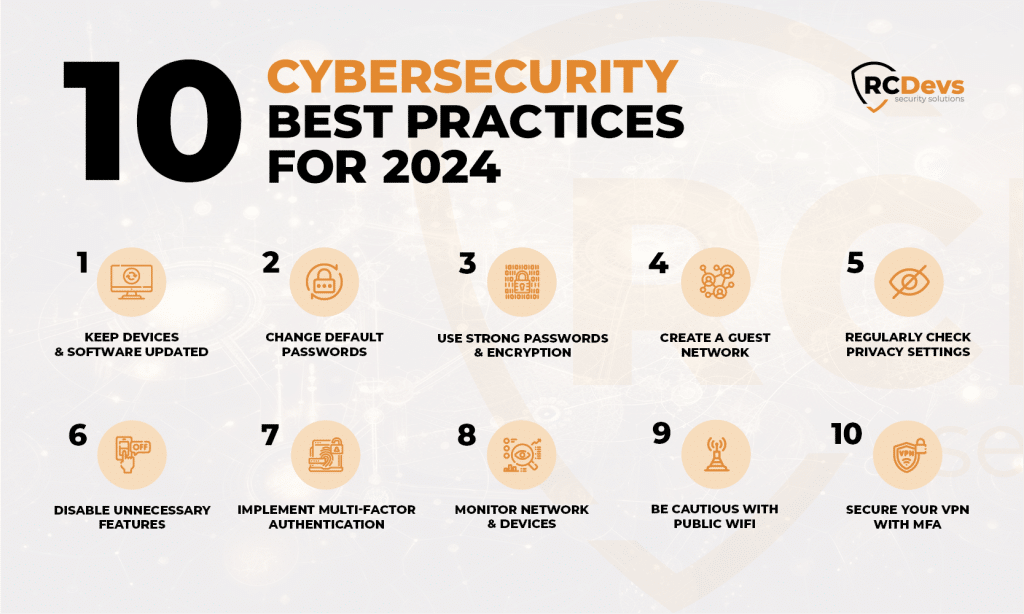
To help ensure the safety of your IoT devices (and your networks), consider these 10 Cybersecurity Best Practices for 2024:
- Keep Devices and Software Updated: Ensure that all IoT devices are regularly updated with the latest firmware and software. Manufacturers often release updates to patch vulnerabilities, so staying current is crucial for maintaining security.
- Change Default Passwords: Many IoT devices come with default passwords, which are often easy for attackers to guess. Changing these to unique, strong passwords is a fundamental step in securing devices.
- Use Strong Passwords and Encryption: Implement strong, complex passwords for all devices and networks. Additionally, use robust encryption methods like WPA2 or later for WiFi networks to protect communications. Of course, securing your Wifi network with MFA is an undeniable advantage.
- Create a Guest Network: If your router allows, set up a separate guest network for visitors. This helps protect your main network from potentially compromised devices that guests may bring.
- Regularly Check Privacy Settings: Review and adjust the privacy and security settings of your IoT devices to ensure they meet your requirements. Default settings may not always provide the best security.
- Disable Unnecessary Features: Turn off any features on your IoT devices that you don’t use. Unused features can provide additional avenues for attackers to exploit.
- Implement Multi-Factor Authentication: Where available, use multi-factor authentication (MFA) for an added layer of security. This requires additional verification beyond just a password, making unauthorized access more difficult.
- Monitor Network and Devices: Keep track of all devices connected to your network and regularly monitor them for any unusual activity, which could indicate a security breach.
- Be Cautious with Public WiFi: When managing IoT devices remotely, be aware of the risks associated with public WiFi networks. Using a VPN can help mitigate these risks.
- Secure your VPN with MFA: Remote working is here to stay! And 2023 saw a rise in VPN vulnerabilities, with almost 50% of organisations reporting an attack related to. Make sure that remote access is just as secure as on-site access.
IV. Cloud Security Developments
1. SaaS Applications and Security Challenges
The expansion of SaaS applications poses significant security risks. With many organizations adopting remote or hybrid work models, there’s an increase in the use of cloud-based solutions for critical operations. This shift expands the attack surface, making SaaS applications a prime target for cyber adversaries. The lack of visibility and control over these applications, coupled with their access to sensitive data, creates significant blind spots. Security teams need to reassess their SaaS security posture, monitor application installations, and manage security controls to prevent major data breaches.
2. Rise of Identity Verification and Proactive Security Tools
In 2024, more organizations will embrace identity verification technologies to ensure the authenticity of employees, partners, and customers during account onboarding. This is especially relevant as AI improves and creates new risks. Companies will also invest more in proactive security tools and technology to detect vulnerabilities and security gaps, moving away from traditional reactive approaches. Technologies such as risk-based vulnerability management, attack surface management, and security posture tools will become increasingly significant.
3. Collaborative Cybersecurity and Quantum Cloud Security
There’s a growing trend towards collaborative cybersecurity, with enterprises prioritizing understanding and responding to potential threats through shared information. Furthermore, the advancement of quantum computing necessitates a shift towards quantum-resistant cryptography, presenting new challenges and paradigms in cloud security.
With the increased risk of data breaches and unauthorized access, organizations are focusing more on deploying robust security measures such as multi-factor authentication (MFA) and access control mechanisms, has become more pronounced. In this context, SaaS tools like the RCDevs OpenOTP Security Suite are gaining attention. Our suite offers a comprehensive solution for enhancing data protection in cloud environments, providing strong MFA and access control features that are essential in today’s security landscape.
As we progress into 2024, these developments in cloud security will play a critical role in shaping how organizations leverage cloud technology while maintaining robust security postures. The focus will be on not only adopting new technologies but also on ensuring compliance, governance, and collaboration to safeguard against emerging threats in the cloud.
V. Data Privacy Trends and Regulations in 2024
As we move through 2024, several key trends and regulations are reshaping this vital domain for businesses and individuals alike.
1. Evolving Data Privacy Landscape
The global data privacy landscape is witnessing significant changes, driven by evolving consumer awareness and expectations and the increasing value of personal data. With data breaches becoming more common, there’s a growing demand for stricter data privacy measures and transparency in how organizations collect, store, and use personal data. This evolving landscape requires organizations to be more accountable in their data handling practices.
2. Impact of Regulatory Compliance
2024 sees a significant increase in data privacy fines, signaling a global shift towards stricter enforcement of data protection laws. Companies like Meta and TikTok have faced record-breaking fines, underscoring the need for stringent compliance.
Compliance with data privacy regulations such as the General Data Protection Regulation (GDPR) in the EU and the California Consumer Privacy Act (CCPA) in the US has become a priority for organizations worldwide. These regulations mandate strict data protection and privacy practices, with significant penalties for non-compliance. Organizations must therefore ensure that their policies and procedures are up-to-date and compliant with these evolving regulations.
3. Unstructured Data Explosion: Managing the Unmanageable
With the rise of GenAI, the volume of unstructured data is skyrocketing. Efficiently managing this data requires sophisticated classification tools and secure storage solutions. Organizations must invest in technologies capable of analyzing and securing vast quantities of unstructured data to prevent unauthorized access and maintain data privacy.
4. Data Sovereignty: The Rise of Localization Laws
Data sovereignty is becoming increasingly important, driven by laws mandating data localization. Multinational corporations must redesign their data management infrastructures to comply with regional data sovereignty requirements, ensuring data is stored and processed in accordance with local laws.
5. Advancements in Data Protection Technologies
To keep pace with the growing data privacy challenges, advancements in data protection technologies are emerging. These include more sophisticated encryption methods, enhanced data anonymization techniques, and AI-driven tools for data privacy management. Implementing such technologies helps maintaining robust data privacy and security.
6. Empowering Consumers
Consumers demand more control over their personal data. In response, companies are adopting privacy-enhancing technologies and consent mechanisms that empower users. Offering user-friendly interfaces for data management and clear consent options is essential for building consumer trust and ensuring compliance.
7. Preparing for Future Privacy Challenges
Looking ahead, organizations must stay informed about the latest data privacy trends and regulatory changes. This involves not only implementing current best practices but also anticipating future privacy challenges and preparing accordingly. Developing a culture of privacy within the organization and ensuring ongoing education and training for employees are critical steps in this direction.
VI. Passwordless Authentication: Will 2024 Mark the Tipping Point?
Passwordless authentication, while presented as a growing tendency for several years, has yet to fully become the standard in cybersecurity practices. However, 2024 might be the turning point for this technology, aligning with the most recent trends and eagerly awaited by the public for its convenience, among both consumers and the workforce. According to Security Magazine, the adoption of passwordless authentication is expected to become a mainstream practice, with its ability to prevent data breaches triggered by weak or compromised passwords being a significant advantage. This shift towards passwordless methods, such as passkeys, biometrics, hardware and software tokens, or public-key cryptography, reflects a broader move towards more secure and user-friendly authentication methods.
The demand for seamless and highly secure authentication methods is growing, not just among enterprises but also consumers. Innovations like Google’s passkeys, which leverage biometric verification, offer a simplified login process by eliminating the need to remember traditional passwords. This transition enhances security while making the authentication process more convenient for users, facilitating a smoother transition to passwordless methods that are considered more user-friendly despite the change in habit they require.
The growing importance of data privacy, coupled with an increasing awareness among consumers about their data rights, further propels the need for more secure authentication methods. Organizations are encouraged to adopt technologies that address privacy concerns from the outset, including passwordless authentication, which can reduce the risk of data breaches and ensure compliance with evolving data privacy regulations.

VII. Zero Trust Architecture Implementation
1. Fundamentals of Zero Trust Architecture
Zero Trust Architecture (ZTA) is based on the principle that organizations should not automatically trust anything inside or outside their perimeters. Instead, they must verify everything trying to connect to their systems before granting access. This approach minimizes the attack surface and reduces the chances of unauthorized access to sensitive data.
2. Implementing Zero Trust in Organizations
For successful implementation, organizations need to adopt a comprehensive strategy encompassing various aspects of their IT environment. This includes robust identity and access management (IAM), micro-segmentation of networks to control access, and rigorous security policies governing data access and usage. The goal is to provide the least privilege access, ensuring users have only the necessary rights to perform their tasks.
3. The Role of Technology in Zero Trust
Advancements in technology play a crucial role in implementing Zero Trust Architecture. AI and machine learning are instrumental in monitoring network traffic and user behavior to detect anomalies that could indicate a security threat. Automation in enforcing access policies and responding to potential threats is also key to an effective Zero Trust strategy. Furthermore, RCDevs’ Presence-Based Logical Access enhances Zero Trust security by mandating physical presence confirmation through badging-in at authorized locations for network access, integrating with multi-factor authentication for rigorous user verification.
4. Challenges and Best Practices
While Zero Trust offers considerable security benefits, its implementation comes with challenges. These include the complexity of redesigning network architecture, the need for comprehensive policy development, and ensuring user compliance. Best practices involve a phased implementation, starting with the most critical data and systems, and a continuous evaluation and adaptation of security policies.
5. Preparing for a Zero Trust Future
As Zero Trust becomes an increasingly essential part of cybersecurity, organizations must start preparing for this shift. This involves not only technological investments but also a cultural change in how security is perceived and managed within the organization.
The evolution of cybersecurity strategies in 2024 is significantly marked by the continued adoption and integration of Zero Trust Architecture (ZTA). This growing emphasis on ZTA is largely a response to the increasingly complex and sophisticated nature of cyber threats, coupled with the demand for more robust and resilient cybersecurity frameworks. The trend towards Zero Trust is expected to maintain its momentum well into 2024 and beyond, reflecting its critical role in addressing the evolving challenges in cybersecurity. As cyber threats become more sophisticated, the traditional ‘trust but verify’ approach is giving way to a more stringent ‘never trust, always verify’ model.
VIII. Defense in Depth (DiD): A Multi-layered Approach to Security that’s Gaining in Popularity
This multi-layered approach to security, rooted in military tactics, is designed to provide redundancy in the event of a system failure or a security breach. The essence of DiD is that multiple layers of defense can significantly reduce the risk of a successful attack.
The Defense in Depth strategy is often likened to a fortified castle, where multiple layers of defense, such as a moat, outer walls, and inner strongholds, provide successive barriers to protect against attacks. Defense in Depth is complementary to Zero Trust Architecture.
The first layer of DiD involves perimeter security, which includes traditional firewalls and intrusion detection systems. As noted in a recent article by CSO Online, perimeter security remains a fundamental aspect of DiD, but it’s no longer sufficient on its own due to the sophistication of modern cyber threats. The article emphasizes the need for organizations to evolve beyond perimeter defense, integrating more advanced technologies like AI-driven threat detection systems.
Moving inward, the next layer focuses on network security. This includes not only the segregation of networks but also the monitoring and controlling of network traffic. A 2024 report by Infosecurity Magazine highlighted the increasing importance of network segmentation in DiD, particularly in thwarting lateral movements within a network by attackers who have breached the perimeter.
The third layer is endpoint security. As pointed out in a recent Forbes article, the rise of remote work and BYOD (Bring Your Own Device) policies has expanded the threat landscape, making endpoint security more critical than ever. This layer involves the use of antivirus software, personal firewalls, and patch management to secure individual devices within the network.
Another crucial layer is application security, which focuses on ensuring that software applications are free of vulnerabilities that could be exploited by attackers. The Harvard Business Review recently published an analysis on the growing importance of application security in the DiD strategy, especially in the context of increasing reliance on cloud-based applications and services.
The final layer of DiD is data security. This layer involves protecting the actual data through encryption, access controls, and data loss prevention techniques. A 2024 study by the Journal of Cybersecurity Research underscored the significance of data-centric security measures in DiD, particularly in light of the General Data Protection Regulation (GDPR) and other data protection laws.
Defense in Depth in 2024 represents a comprehensive and nuanced approach to cybersecurity. It acknowledges that no single defense measure is infallible and that a layered, multifaceted approach is essential for robust security. As cyber threats continue to evolve, so too must our strategies for defense, making DiD more relevant than ever in the current cybersecurity landscape.
More infos about DiD here.

IX. The Cybersecurity Workforce and Skill Shortage
In 2024, the cybersecurity landscape is not only defined by technological advancements and emerging threats but also by the human element – the cybersecurity workforce. The industry continues to grapple with a significant skills shortage, a challenge that impacts the ability of organizations to effectively defend against cyber threats. A cybersecurity workorce study, published by ISC2, highlights current and future challenges for 2024.
1. Magnitude of the Workforce Shortage
The gap in the cybersecurity workforce is more than a numbers issue; it’s a matter of expertise. There is an increasing demand for skilled professionals who can navigate the complex and evolving landscape of cyber threats. This shortage is not just about filling positions; it’s about equipping the cybersecurity sector with the right talent capable of handling sophisticated and evolving threats. As we head into 2024, this trend shows no signs of slowing down. The cybersecurity workforce reached its highest number ever in 2023, with 5.5 million professionals. However, despite this growth, there remains a significant shortfall in the workforce, with a need for an annual growth rate of 12.6% to effectively address threat landscape challenges. Unfortunately, in 2023, this growth was only 8.7%.
2. Addressing the Skill Gap
To mitigate this challenge, organizations and educational institutions are focusing on developing talent through targeted training programs, cybersecurity certifications, and awareness campaigns. Emphasis is being placed on equipping professionals with the skills needed to handle current and emerging cyber threats, including understanding advanced technologies such as AI and machine learning.
3. The Role of Automation and AI
Automation and AI are also seen as potential solutions to the workforce shortage. By automating routine tasks and leveraging AI for threat detection and response, cybersecurity teams can focus on more complex and strategic aspects of security. However, this technological aid is not a substitute for human expertise but rather a complement to the skills of cybersecurity professionals.
4. Preparing for Future Workforce Needs
Looking forward, the industry needs to anticipate future skills requirements and adapt its workforce development strategies accordingly. This involves not only technical training but also fostering soft skills such as problem-solving, critical thinking, and effective communication, essential for the modern cybersecurity professional.
X. Charting the Path Forward: Final Reflections on Cybersecurity in 2024
In synthesizing these trends, it’s clear that the path forward in cybersecurity for 2024 and beyond lies in embracing innovation, fostering collaboration across sectors, and developing a culture of continuous learning and adaptation. Organizations must not only adopt the latest technological tools but also cultivate a deep understanding of the evolving threat landscape and the interconnectedness of digital ecosystems. The journey through the cybersecurity terrain is complex and fraught with challenges, yet with a strategic, informed, and agile approach, we can navigate these uncertainties and emerge more resilient in the face of ever-evolving cyber threats.
For a deeper dive into these trends, we invite you to also read the latest insights from G2 Research.

