
Closing Entra ID MFA Gaps with RCDevs OpenOTP
Closing Entra ID MFA Gaps with RCDevs OpenOTP
The Current Identity Reality
Today’s businesses are using a mix of SaaS applications, legacy systems, hybrid workstations, and remote access tools. Microsoft Entra ID (Azure AD) and Office 365 form the backbone of most cloud identity strategies and include native multi-factor authentication (MFA), FIDO2, and Conditional Access. Yet this does not fully solve every authentication and access control problem companies face:
- Windows endpoint authentication: native cloud MFA does not extend to Windows login screens.
- Offline workstation access: users need secure logins even without network connectivity.
- Legacy and protocol-limited systems: RADIUS, LDAP, on-prem portals and applications do not inherently support modern MFA flows.
- Consistent policy enforcement across environments: cloud MFA policies are powerful, but do not natively unify on-prem, legacy, and endpoint authentication contexts.
This is where RCDevs WebADM and the OpenOTP, including the OpenOTP Credential Provider for Windows, fill key gaps in a comprehensive identity architecture.
What RCDevs WebADM & OpenOTP Solve
WebADM is a web-based identity service platform that manages user identities and controls access to systems through authentication policies. It integrates with enterprise directories and applications to centralize authentication workflows, apply security policies, and orchestrate identity-related services across environments.
OpenOTP is the multi-factor authentication server built on top of WebADM. It enables modern authentication methods such as FIDO2/passkeys, push notifications, OTP, smartcards, Magic Links, and others, which are enforced through WebADM’s policy engine.
Together, WebADM and OpenOTP provide a centralized authentication layer that helps organizations manage identities and secure access to both cloud and on-premises systems.
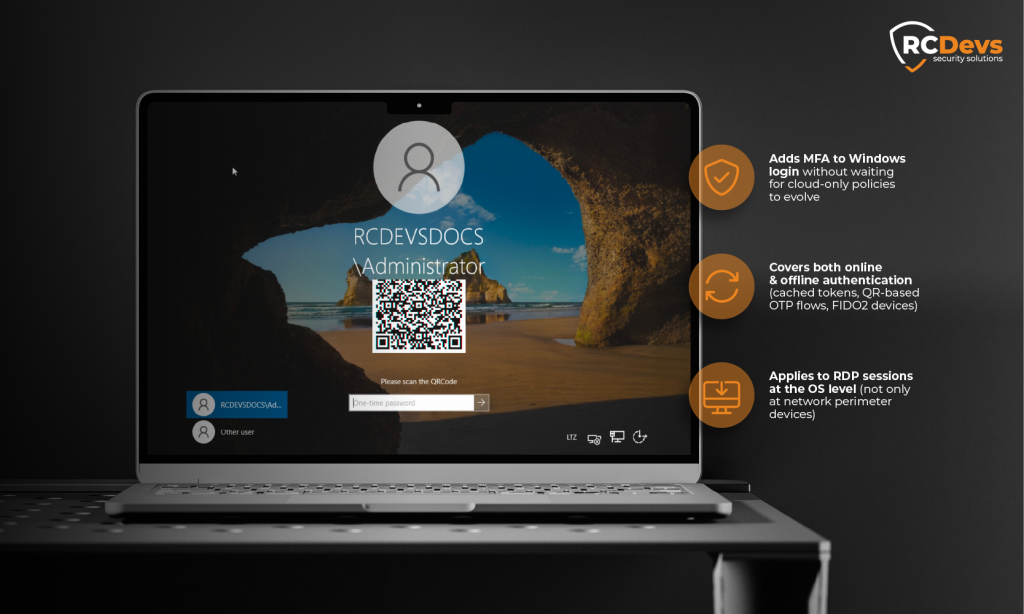
1. Extending MFA to Windows Login & RDP
Problem: Microsoft Entra ID’s cloud MFA does not natively protect Windows workstation and Remote Desktop (RDP) logins. You can enforce MFA for accessing Azure and cloud apps, but a stolen or weak local credential still gets you into a workstation or RDP session.
RCDevs Solution: The OpenOTP Credential Provider for Windows integrates OpenOTP into the Windows authentication stack. It plugs into the Windows credential provider mechanism so that users must complete an OpenOTP MFA check (OTP, push, FIDO2, smartcard, etc.) during Windows domain or local login.
This solves a real operational gap:
- Adds MFA to Windows login without waiting for cloud-only policies to evolve
- Covers both online and offline authentication: if a device is off the network, users can still authenticate using cached tokens, QR-based OTP flows, or FIDO2 devices.
- Applies to RDP sessions protected at the operating system level rather than purely at network perimeter devices
This capability is distinct from Entra ID MFA because it happens before network connectivity with cloud happens, securing the endpoint itself.
2. Consistent MFA Across Cloud & Legacy Protocols
Problem: Entra ID MFA is great for SSO and Conditional Access in cloud applications, but not all enterprise access points understand or can enforce those cloud MFA policies. Legacy LDAP applications, RADIUS-only clients (e.g., VPN, NAC), or proprietary login portals often lack built-in support for modern MFA.
RCDevs Solution: OpenOTP and WebADM act as a unifying MFA backend:
- RADIUS bridge: allows traditional RADIUS-based systems to enforce MFA (OTP, Push, FIDO2) without native support.
- LDAP integration: intercepts and extends legacy LDAP bind authentication with MFA challenges.
- WebAuthn/FIDO2 supported across web and endpoint contexts, not just in the cloud.
This means an organization can have one MFA decision engine, WebADM/OpenOTP, feeding both cloud (via federation/EAM) and non-cloud authentication flows, ensuring consistency and easier policy governance.

3. Enhanced Azure/Entra ID Integration
Problem: Native MFA in Entra ID is bound by Microsoft’s implementation and interface limitations. Conditional Access policies are powerful, but cannot always express complex authentication requirements for hybrid and legacy access surfaces.
RCDevs Solution: Entra ID supports External Authentication Methods (EAM) where the MFA decision is delegated to a third-party identity provider. RCDevs can act as that provider, returning authentication method claims (e.g., OTP, FIDO2) back to Entra ID. This lets organizations:
- Use their own MFA decision logic and policies while still using Entra ID for access governance.
- Maintain consistent authentication flows whether users log into cloud apps or on-prem systems
- Synchronize cloud directory objects into WebADM for consistent identity handling and policy application across environments. (RCDevs | Documentation Center)
This approach increases flexibility. You are not locked into a single vendor’s MFA implementation for all authentication contexts.
4. Operational and Security Advantages
While not directly tied to cloud providers, RCDevs components add tangible benefits:
- Inline token enrollment at first Windows login: reduces deployment friction by letting users register MFA tokens without separate portals.
- Offline login support: crucial for mobile workers or remote sites without Internet connectivity.
- Multiple authentication methods: choice of OTP, push, FIDO2/passkeys, smartcards, and more, all managed in a centralized policy engine.
These capabilities complement Entra ID’s cloud controls by covering scenarios where cloud MFA is not directly involved or visible, such as workstation access, offline use, or legacy network protocols.
Why Keep RCDevs Even If You Use Entra ID MFA
Microsoft Entra ID provides excellent cloud authentication and Conditional Access policies, but it does not, on its own, cover the full spectrum of enterprise access points:
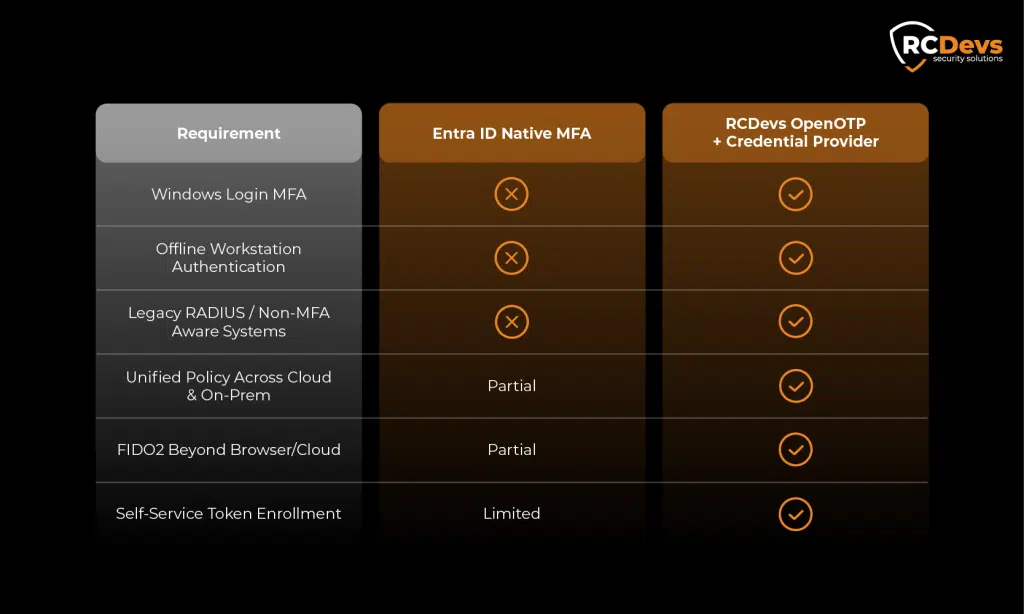
By retaining an RCDevs IAM/MFA layer, organizations can:
- Extend strong authentication to places where cloud policies do not reach
- Maintain consistent controls even offline
- Integrate modern methods in legacy and hybrid access points
- Avoid fragmentation between cloud MFA and on-prem authentication
A Broader Identity Architecture
Modern identity and access management are no longer just about cloud login screens. Companies must secure endpoints, networks, legacy systems, and hybrid environments without compromising policy consistency or user experience.
RCDevs WebADM and OpenOTP, particularly the Windows Credential Provider, address authentication gaps that Entra ID’s native controls do not cover, such as Windows logon, offline access, and legacy protocols. When deployed on-premises, WebADM can also function as an independent authentication authority, allowing users to continue authenticating even during cloud identity outages or connectivity failures. Used alongside Entra ID, this approach provides consistent authentication policies across endpoints, legacy systems, and cloud services while reducing reliance on a single identity control plane.

